Identity used to be simple—users, passwords, and known access points.
That world is gone.
Today, machine and agentic identities outnumber humans, expanding the attack surface at an unprecedented scale. AI agents, APIs, bots, and service accounts are constantly interacting across systems—and each one represents a potential risk if not properly governed.
This shift is at the heart of Identity Management Day 2026. The question now is no longer just who has access—but what.
And most organizations still don’t have a clear answer.
The Identity Perimeter Has Dissolved
For years, identity security was synonymous with access control: make sure the right employees can log in, and keep everyone else out. Multi-factor authentication was the gold standard, and for a long time, it was enough.
It no longer is. The challenge today is not just authentication — it is visibility, control, and orchestration across an increasingly complex identity ecosystem.
A typical organization now manages not just employees and customers, but also contractors, APIs, service accounts, AI agents, and automated workflows—often numbering in the thousands.
Identity crime often succeeds not because attackers are unstoppable, but because everyday systems make it too easy to guess, reuse, steal, or reset credentials. When those systems include non-human actors operating at machine speed, the consequences of a single misconfigured identity can cascade faster than any human response team can contain.
Three Identity Risks Business Leaders Cannot Afford to Ignore

1. The non-human identity blind spot
Most organizations have reasonable visibility into their human identities. They know their employees, manage their accounts, and offboard people when they leave. Non-human identities are a different story.
API keys get created and forgotten. Service accounts accumulate privileges over time. AI agents are deployed into production workflows without formal identity governance. In a world where machine identities tremendously outnumber humans, thinking that implementing multi-factor authentication alone solves all of your identity problems simply does not cut it anymore.
The first step is inventory. You cannot govern what you cannot see. Creating a single, current view of every identity in your environment — human, machine, and agentic — is the foundation on which everything else is built.
2. Synthetic identity fraud is scaling with AI
Synthetic identity fraud involves stitching together a mix of real and fake information to create a "new" identity that can pass basic checks. This type of fraud has always been difficult to detect. Generative AI has made it significantly easier to produce.
For organizations that rely on identity verification during customer onboarding, account recovery, or transaction processing, the bar for what constitutes a reliable identity check has risen sharply. Deepfake-driven impersonation, AI-generated documentation, and synthetic profiles that pass surface-level validation are no longer theoretical threats. They are operational ones.
The organizations most exposed are those whose identity verification processes were designed for a world where fraudulent identities required significant effort to construct. That world no longer exists.
3. Access that outlives its purpose
Identity risks in workplaces include employees, contractors, or vendors who have access they no longer need, or who were never properly limited in the first place. This is one of the oldest problems in identity management, and it remains one of the most common causes of preventable breaches.
The combination of cloud migration, remote work, and rapid AI adoption has accelerated the problem. Roles change faster. Projects spin up and wind down. Tools are adopted and abandoned. Each transition leaves behind access entitlements that nobody explicitly revoked — and that an attacker, or a compromised account, can exploit.
Identity governance is not a one-time exercise. It is a continuous process of reviewing who has access to what, ensuring it is still appropriate, and removing it when it is not.
What Good Identity Management Looks Like in 2026
The organizations that are ahead of this challenge share a few common practices:
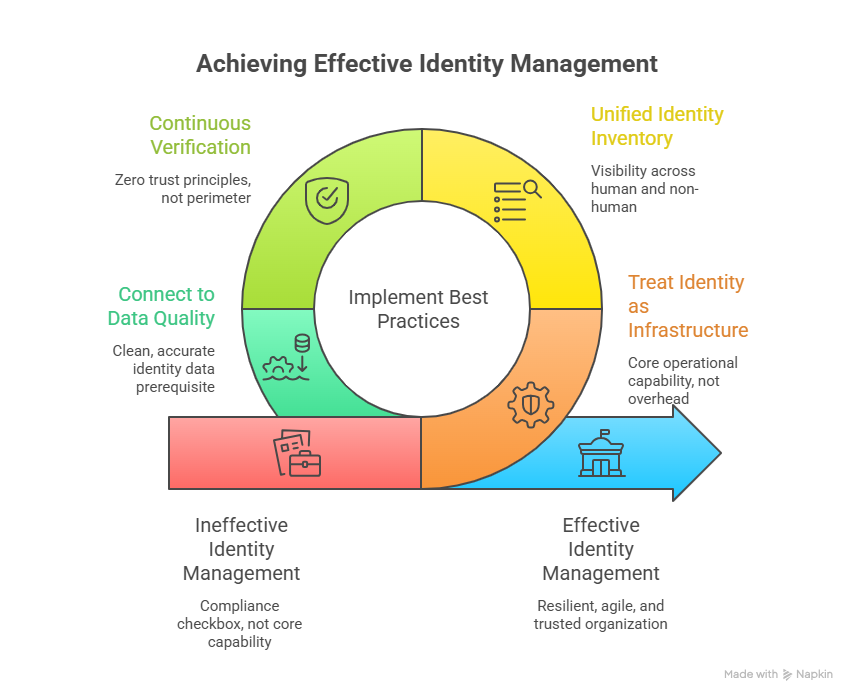
They treat identity as infrastructure, not IT overhead. Identity governance is not a compliance checkbox. It is a core operational capability that touches every system, every workflow, and every customer interaction. Organizations that invest in it accordingly are more resilient, more agile, and more trusted.
They have visibility across human and non-human identities. A unified inventory of all identities in the environment — including service accounts, API keys, bots, and AI agents — is the starting point for any meaningful governance program. Without it, you are managing the part of the iceberg that is above water.
They build for continuous verification, not perimeter defense. Zero trust principles — verifying every access attempt based on identity, device posture, and context — have replaced perimeter-based models as the foundation of identity security. This shift requires investment, but it also reflects how modern organizations actually operate: across clouds, devices, and geographies that have no meaningful perimeter.
They connect identity to data quality. An identity program is only as strong as the data underlying it. Duplicate records, stale attributes, and inconsistent identity data across systems create gaps that attackers find before governance teams do. Clean, accurate identity data is not a nice-to-have — it is a prerequisite for effective security and reliable identity verification solutions.
Identity Management Day Is a Starting Line, Not a Finish Line
Identity Management Day was established to educate business leaders and IT decision makers on the risks of new identity vectors and the dangers of not properly securing identities and access credentials. It is a moment to pause, assess, and recommit to the work — not a one-day event that substitutes for a year-round program.
For business leaders, the conversation to have today is not "are we compliant?" It is "do we know every identity in our environment, do we know what it can access, and do we know that access is still appropriate?"
If the honest answer to any of those questions is "not entirely" — that is where the work begins.
The identity landscape has never been more complex. The consequences of getting it wrong have never been more significant. And the tools and practices to get it right have never been more accessible.
For organizations looking to strengthen identity security and prevent fraud across every interaction, investing in robust identity verification capabilities is critical—explore how modern solutions can support this here: https://www.melissa.com/en-au/identity-verification
There is no better day to start than today.
Identity Management Day, observed annually on the second Tuesday of April, is led by the Identity Defined Security Alliance (IDSA) in partnership with the National Cybersecurity Alliance—bringing global attention to the importance of securing digital identities.